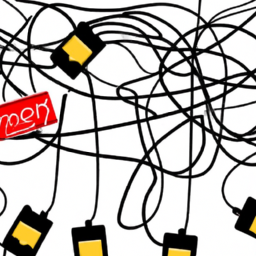
Welcome to the intricately woven world of web hosting, where firewalls act as the guardians of your digital kingdom. Picture yourself navigating through a maze, each turn representing a potential roadblock for incoming traffic. As you strive to unlock the full potential of your website, the firewall maze becomes a formidable challenge to conquer.
In this article, we will delve into the depths of the firewall maze, equipping you with the knowledge to unblock incoming traffic. With a technical, analytical, and detail-oriented approach, we will guide you through the labyrinth, ensuring your website can freely communicate with the outside world.
You will begin by understanding the basics of firewalls, unraveling their purpose and functionality. From there, we will help you identify the blocked traffic and teach you how to adjust firewall settings accordingly.
To ensure you only receive traffic from trusted sources, we will explore the concept of whitelisting and the use of VPNs or proxies.
But the journey doesn’t end there. We will emphasize the importance of regularly monitoring and updating your firewall settings to safeguard against evolving threats. Get ready to navigate the firewall maze and unleash the true potential of your web hosting experience.
Key Takeaways
- Navigating through a firewall maze is necessary to unblock incoming traffic in web hosting.
- Adjusting firewall settings is crucial to allow desired content through and secure incoming traffic.
- Regularly monitoring and updating firewall settings is essential to detect vulnerabilities and unauthorized access attempts.
- Implementing IP filtering and whitelisting trusted sources enhances web hosting security.
Understand the Firewall Basics
Get ready to dive into the nitty-gritty of web hosting by understanding the basics of how firewalls work to unblock incoming traffic.
Firewall configuration plays a crucial role in determining what traffic is allowed into your website. By setting up rules and filters, you can control which IP addresses or ports are permitted access.
It’s important to be aware of common firewall vulnerabilities, such as misconfigured rules or outdated software, which can leave your website vulnerable to attacks.
Identifying the blocked traffic is the next step in the process, where you analyze the firewall logs to determine which requests are being denied. This information will help you troubleshoot and make the necessary adjustments to ensure that legitimate traffic is not blocked.
Identify the Blocked Traffic
Discover the hidden pathways that prevent your desired content from reaching its destination. Identifying blocked traffic can be a complex process, requiring troubleshooting steps to uncover the root cause.
There are several common reasons for blocked traffic that you should be aware of:
-
Misconfigured firewall rules: Incorrectly configured firewall rules can unintentionally block incoming traffic.
-
IP address restrictions: If your firewall is set to only allow traffic from specific IP addresses, it may be blocking legitimate requests.
-
Port blocking: Certain ports may be blocked by default, preventing incoming traffic on those ports.
-
Denial of Service (DoS) attacks: Malicious attempts to overload your server with traffic can result in legitimate requests being blocked.
Now that you have identified the blocked traffic, it’s time to adjust your firewall settings to allow the desired content through.
Adjust Firewall Settings
To ensure that your desired content can flow freely, simply tweak the settings of your protective barrier. Adjusting the firewall settings is a crucial step in troubleshooting firewall issues and implementing best practices for securing incoming traffic. By customizing the firewall rules, you can allow specific types of traffic while blocking potentially harmful ones.
To illustrate this process, consider the following table:
| Source IP | Protocol | Port |
|---|---|---|
| 192.168.1.1 | TCP | 80 |
| 10.0.0.1 | UDP | 443 |
| 172.16.0.1 | TCP | 22 |
In this example, the firewall is configured to allow incoming traffic from three trusted sources. The Source IP column represents the IP addresses from which traffic is permitted, the Protocol column indicates the communication protocol used, and the Port column shows the specific port number being allowed.
By adjusting your firewall settings as needed, you can effectively unblock incoming traffic and ensure the desired content reaches its intended destination. In the next section, we will discuss how to whitelist trusted sources without compromising security measures.
Whitelist Trusted Sources
Allow only your most trusted sources to pass through the protective barrier, creating a secure pathway for your content to flow freely. Implementing IP filtering is a crucial step in this process. By carefully selecting and whitelisting specific IP addresses or ranges, you can restrict incoming traffic to only those sources you trust implicitly. This not only enhances your web hosting security but also minimizes the risk of unauthorized access or malicious activities.
Additionally, configuring advanced firewall rules adds an extra layer of protection. With these rules, you can define specific criteria for allowing or blocking incoming traffic based on factors such as port numbers, protocols, or even specific keywords. By implementing these measures, you can ensure that your web hosting environment remains secure and shielded from potential threats.
Transitioning into the next section, considering the use of VPNs or proxies can further enhance the security of your web hosting infrastructure.
Use VPNs or Proxies
Using VPNs or proxies can further bolster the security of your web hosting setup, providing an additional layer of protection against potential threats. When it comes to unblocking incoming traffic, there are several factors to consider in choosing between VPNs and proxies.
Here are three key points to help you make an informed decision:
-
Comparing VPNs and proxies for unblocking incoming traffic:
- VPNs create an encrypted connection, ensuring secure data transfer.
- Proxies act as intermediaries, hiding your IP address and providing anonymity.
- Both VPNs and proxies can bypass restrictions and access content from different locations.
-
Pros and cons of using VPNs and proxies in web hosting:
- VPNs offer enhanced security but may slow down connection speeds.
- Proxies are faster but may not provide the same level of encryption.
- VPNs require installation and configuration, while proxies are easier to set up.
With the knowledge of VPNs and proxies, you can now delve into the next section on regularly monitoring and updating firewall settings to maintain a secure web hosting environment.
Regularly Monitor and Update Firewall Settings
Regularly keeping an eye on and updating your shield settings is crucial to ensure a safe and sound online fortress. Continuous monitoring of your firewall is essential to detect any potential vulnerabilities or unauthorized access attempts.
By regularly checking your firewall logs and analyzing the incoming traffic patterns, you can identify any suspicious activities or potential threats. It is also important to implement automated updates for your firewall software to ensure that you have the latest security patches and features. These updates help in addressing any known vulnerabilities and enhancing the overall protection of your web hosting environment.
By staying proactive and regularly updating your firewall settings, you can effectively safeguard your website and ensure a secure online presence.
Frequently Asked Questions
What are the potential risks of unblocking all incoming traffic in web hosting?
Unblocking all incoming traffic in web hosting can pose several potential risks. Firstly, it exposes your server to malicious attacks, such as DDoS or SQL injection.
Secondly, it increases the chances of unauthorized access to sensitive data, potentially leading to data breaches.
To mitigate these risks, it’s crucial to implement strict access controls, regularly update security patches, and employ intrusion detection systems.
Additionally, utilizing a web application firewall can help filter out malicious traffic and protect your hosting environment.
How can I identify the specific IP addresses that are being blocked by my firewall?
To identify specific IP addresses being blocked by your firewall, you can utilize effective troubleshooting methods and tools.
Start by analyzing incoming traffic using network monitoring tools like Wireshark or tcpdump. Look for patterns or anomalies in the traffic data that might indicate potential security threats.
Additionally, review firewall logs and examine any blocked IP addresses or connections. By combining these techniques, you can successfully identify and resolve issues with blocked IP addresses.
Are there any limitations or compatibility issues when adjusting firewall settings for different types of web hosting platforms?
When adjusting firewall settings for different types of web hosting platforms, there can be limitations and compatibility issues to consider. These may arise due to differences in firewall software, configurations, and network infrastructure.
Some platforms may have specific firewall requirements or restrictions that must be followed. It’s important to thoroughly research and understand the specific limitations and compatibility issues of the web hosting platform you’re working with to ensure proper firewall adjustments and optimal security.
Is it possible to whitelist multiple sources at once, or do I need to manually enter each IP address separately?
Whitelisting multiple sources can be a daunting task, but fear not! With the power of automation, you can save yourself from the tedious process of manually entering each IP address separately. By leveraging advanced firewall rules, you can easily whitelist multiple sources at once.
This not only saves time but also allows for efficient management of incoming traffic. So sit back, relax, and let automation be your guide through the complex world of firewall settings.
What are some best practices for regularly monitoring and updating firewall settings to ensure optimal security?
To ensure your firewall settings are up to date and effective in protecting your web hosting, regularly monitor and update them.
Review your firewall rules frequently, ideally on a monthly basis, to stay ahead of potential threats.
Keep an eye on security advisories and news to stay informed about emerging vulnerabilities.
Additionally, consider implementing an automated system that regularly scans and updates your firewall settings to ensure optimal security at all times.
Conclusion
Congratulations! You’ve successfully navigated the treacherous labyrinth of the firewall maze. Just like a skilled adventurer, you’ve learned the basics, identified and adjusted settings, and even whitelisted trusted sources.
By utilizing VPNs or proxies, you’ve outsmarted the most cunning adversaries. Your dedication to regularly monitoring and updating firewall settings has paid off, ensuring the utmost security for your web hosting.
Remember, the firewall maze may be complex, but with knowledge and persistence, you can conquer any challenge that comes your way. Stay vigilant, and may your web hosting journey be safe and prosperous.